War is both timeless and ever changing. While the basic nature of war is constant, the means and methods we use evolve continuously. Actions by a nation-state to penetrate another nation’s computers or networks for the purposes of causing damage or disruption can be termed as cyber warfare. Strategic cyber-attacks could be on a nations critical primary infrastructure and utilities, whilst operational cyber-attacks are against adversary’s military. A very comprehensive definition of cyber warfare could be “The strategic, operational, and tactical level action across the spectrum during peace, crisis escalation, conflict, war termination and restoration, waged between competitors, adversaries or enemies using information means to achieve their objectives.” It can include denying battlefield commanders information, keeping sensitive messages secret, spreading propaganda, traditional hacking and so on. Defensive cyber operations would be to protect information in any form, maintain its confidentiality, integrity and availability. The aim of information warfare is to: “corrupt, deny, degrade and exploit adversary information and information systems and processes while protecting the confidentiality, integrity and availability of one’s own information”. Cyber warfare involves targeting computers, online control systems and networks and grids of national utilities and of military. It involves both offensive and defensive actions. Unlike conventional war-fighting which requires logistically supported standing armed forces with kinetic weapons, the cyber attack can be initiated from a single computer by a single operator at an unknown remote location. The disruptive power of cyber warfare has been well established and therefore all major countries are building capabilities for both protective and offensive purposes.
The number of cyber security incidents has been gradually increasing in India. These incidents include phishing, website intrusions and defacements, virus and denial of service attacks among others. Pakistani hackers compromised 10 Indian websites which included National Aeronautics Ltd, Army Institute of Management and Technology, Defence Institute of Advanced Technology, and the Board of Research in Nuclear Sciences. Indian Government took the first formalized step towards cyber security in 2013, by formulating National Cyber Security Policy (NCSP).
The tri-service Defence Cyber Agency (DCA) of the Indian armed forces Headquartered in New Delhi was established in on 28 September 2018. DCA is tasked with handling cyber security threats, and it draws personnel from all three branches of the Services. It is a major step based on the recommendations of the Kargil Review Committee, and indicates the seriousness India finally attaches to cyber threat and its fallouts. The Defence Cyber Agency (DCA) will work in coordination with the National Cyber Security Advisor (NCSA). Meanwhile, as PM Modi is driving the Digital India campaign to harness the great potential for quick transparent governance to deliver efficient services and ensure public security, he has been quick to caution that “clouds of a bloodless war are hovering over the world; someone can steal our digital data, clean up our bank accounts or attack the basic amenities; we have to accept the challenge to ensure cyber security”. Any disruption of such well connected services can play havoc worse than the atomic bomb.

Cyber Domain
To make sense of cyber warfare requires understanding the cyber domain, and accurately defining the cyber environment. Operational planning must take into account the spectrum of threats. Understanding the complexity of implications and the intentions of actors will help develop effective cyber warfare strategies. Cyber domain includes the Internet’s architecture, devices connected to the Internet, and wired and wireless networks. Rather than existing within finite borders, it mimics other natural systems such as bacterial colonies and expanding galaxies, where billions of nodes expand in all directions. Complexity also stems from the exponential growth of computing power and the number of devices connected. As of 31 December 2019, 4,57 billion (58.7%) of the 7.8 billion population of the world was connected on internet. There were nearly 1 billion web hosts with over 25 billion pages. Over 3.5 million blog posts are published on the Internet every day. Over 500 million tweets are sent and over 3.5 billion Google searches are made every day.

Since the cyber domain was designed for openness, security is not inherent in the system. Networks and the software built on top of them ride on an inherently open backbone, and as a result, multiple layers of security need to be built in to ensure system and data integrity. Vulnerabilities are akin to deficiencies in the human immune system. Several characteristics of the cyber environment shape cyber warfare, including rising levels of convergence (single device for many activities), the speed of interactions, the inextricable human element, and the empowerment of the individual within the cyber domain. Enforcing security measures such as installing anti-virus software, creating hard passwords etc all fall as task on the individual. Things happen at the speed of light and therefore any action in cyberspace can be faster and lead to far reaching geographic effects than in other domains. Military has to realize that electrons are much faster than ground forces. Because knowledge transmission is now nearly costless, individuals in loose networks can rapidly learn the most effective attack techniques and exploit previously unknown vulnerabilities. Because of the open design of the cyber domain, defence is inherently more costly and time consuming than offensive. Asymmetry in the cyber domain generally favors smaller and more agile actors. These actors often don’t have a permanent physical address and can mask their virtual ones. This is a key point in order to develop effective mitigation strategies.
Types of Threat
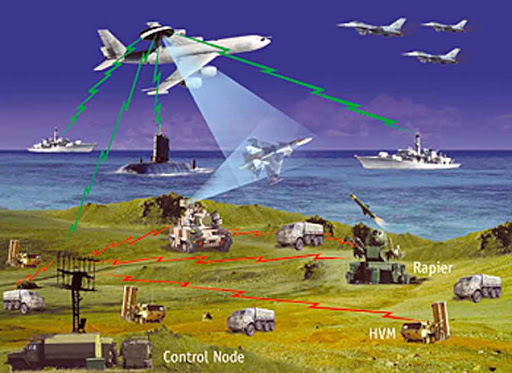
Cyber warfare can present a multitude of threats. At the most basic level, cyber attacks can be used to support traditional warfare. For example, tampering with the operation of air defences via cyber means in order to facilitate an air attack. Soft threats could be espionage and propaganda. There have been many cases of international electronic eavesdropping in the recent years such as stealing personal data by Chinese, and spying by US agencies against even partner nations as revealed by Edward Snowden. Sabotaging military C4ISTAR networks or civilian utilities is part of sabotage. Denial-of-service attack typically by targeting sites or services hosted on high-profile web servers such as banks, credit card payment gateways etc. Massive power outage caused by a cyber attack could disrupt the economy, distract from a simultaneous military attack, or create a national trauma. Cyber propaganda is an effort to control information in whatever form it takes, and influence public opinion. It is a form of psychological warfare through use of social media or fake news websites. It is a form of warfare that seeks to de-legitimize the political and social system on which our military strength is based.
Cyber Attack Modus Operandi
The distributed nature of internet based attacks means that it is difficult to determine motivation and attacking party, and it is unclear when a specific act should be considered an act of war. All militaries are now hiring cyber-warfare experts to defend critical networks and security of sensitive information. Hacktivists or cyber-terrorists use their knowledge and software tools to gain unauthorized access to computer systems they seek to manipulate or damage often just to draw attention to their cause. Cyber has a great scope for industrial espionage.

Political Will
The execution of any kind of war is ultimately a contest of political will. Even cyber terror acts are designed to achieve some political objective, even to demoralize a populace or forcing a government to negotiate. Political objectives must be clear for the ultimate goal of cyber warfare. Whether or not a “Cyber 9/11” will happen, countries must prepare. Deterrence has to be built.
Military Effects and Approach
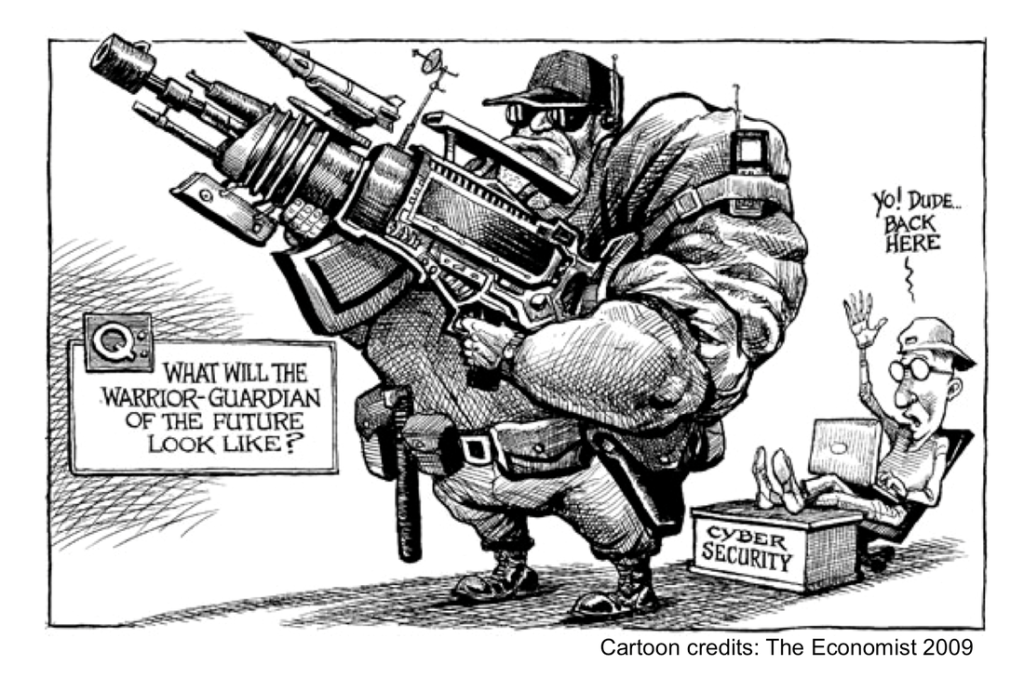
Historical approaches to achieving superiority in the air, land, and sea domains may no longer be valid. The worldwide flood of powerful, inexpensive, and readily available commercial technology is mandating a much more sophisticated approach to military affairs. Computer processing power has been doubling every two years. In the new security environment, the pace of cyber, directed energy, nanotechnology, robotics, and biotechnology advancements is far beyond the normal capacity to predict their effects. Advanced information technology is also changing our perspectives of multi-domain interdependence. Ability to project conventional power is eroding swiftly as state and non-state actors acquire advanced capabilities to offset the military’s strength. Unable to compete with powerful militaries, adversaries are leveraging technological advances to create their own asymmetric advantages. Numerous countries are working on high-powered microwave (HPM), directed-energy, and electromagnetic pulse (EMP) weapons that could destroy electronic systems.
Over 40 percent of the world’s active satellites are in low Earth orbit. Adversaries can deliver effects from EMP through a multitude of nonnuclear modes that produce a wide array of outcomes ranging from temporary interference to system destruction. Other targets include ballistic missiles, submarines, aircraft, as well as man-packed systems. Militaries are also investing in inexpensive low-power jammers to inhibit the positioning, navigation, and timing necessary for effective strike operations. On the other hand advances in technology are improving adversary’s ability to defend. Integrated air defense systems are becoming increasingly resistant to electronic suppression by using passive sensor technologies such as infrared search and track. These technology leaps are being augmented with surface-to-air missiles that have advanced tracking and longer ranges.
Cyber & Space Critical Combination
Denial access to vital satellites that are needed for intelligence, surveillance, and reconnaissance, communications, early warning, and navigation, could severely affect a Commander’s planning, decision, and execution cycle and could render operations in the air, on land, and at sea ineffective. Space allows virtually unimpeded access to monitor missile-launch detection and missile tracking. Space systems have varying degrees of vulnerabilities. Satellites are nearly impossible to hide. They move along predictable paths, that can’t be changed easily. Adversaries can employ a variety of attack options, including kinetically striking the ground stations, jamming or spoofing links, and using directed energy to dazzle or partially blind the satellite. ‘Parasitic microsatellites’ could latch onto a satellite and disable it, alter its orbit, or hijack the information gathered by it. EM Spectrum (EMS) is the sole medium for transmitting and receiving information and signals in space. The frequency bands that space-based systems use within the spectrum are fixed and cannot be changed after launch. One of the key constraints of this battle-space is that only 1 percent of the spectrum accounts for 90 percent of its military and civilian use. The effectiveness of the EMS is also complicated by electromagnetic interference between systems, EMP, and natural phenomena such as lightning, solar flares, and precipitation. Commanders must understand how to operationally assess the impact of forfeiting these systems and employ other capabilities. Consequently, military’s foundational principle of ‘centralized control and decentralized execution’ will be forced to shift to a distributed-control approach that adapts to operational changes. Local superiority in combinations of domains is now required.

Hybrid Response Approach
Cyber warfare touches all warfare domains – ground, sea, air, and space. The economic dimension is also significant. It could result literally in “death by a thousand cuts”. There is a need to address cyber vulnerabilities, increase information flow options, intelligence efforts, and coordinate security through prevention, adaption and appropriate reaction. Need to continually educate all military and civilian stakeholders in addition to securing the networks and nodes themselves. It is also critical to educate average citizens about enhancing the security of their own computers and networks. Education should include resilience training, hands-on scenario response, as well as technical and social engineering. While the vastness of the cyber domain could overwhelm any nation, collective understanding could improve response.
Cyber Weapon’s Life Cycle and Vulnerabilities
Vulnerabilities that the cyber weapon relies on may be removed by manufacturer at any time. Once used, the signature of the weapon can be added to detection systems and blocked. Cyber weapons do not self-destruct and can be reverse engineered. Seizing the initiative means finding the zero day vulnerability and exploiting it before the enemy reacts. Retaining the initiative translates to constantly looking for new vulnerabilities, or finding back doors to ensure multiple paths into a system. While Shanghai Cooperation Organization (SCO) has shown interest in regulating cyber warfare and a collaborative effort between the SCO and NATO could produce more globally acceptable results, the technology is so expansive that any list of banned cyber weapons would be obsolete within days.
The New Multi-domain Imperative
The militaries face a new reality – one with “multi-domain” challenges. The way military builds its force, integrates its planning, and synchronizes its operations must change quickly. In modern military lingo, there are five inter-related domains: land, maritime, air, space, and cyberspace. The cyberspace domain is wholly man-made and is ever-changing. In the emerging ‘multi-domain reality’, an attack will often come from multiple domains simultaneously: jamming of radios and data-links, persistent surveillance, and precise, long-range fires. Military needs to instill in its commanders the ability to deal with ambiguity and incomplete information — the fog of war in the digital age — yet continue to operate in a manner consistent with the intent. Force posture, power projection, and presence in all domains will require greater integration of all services and agencies. The services are unfortunately still reluctant to trade proficiency in their core competencies for futuristic-sounding but potentially empty promises of multi-domain prowess. This will have to change.
International Cyber Warfare Evolves
In the 2006 war against Hezbollah, Israel allegedly used cyber-warfare was part of the conflict. Israel attaches growing importance to cyber-tactics, and along with the U.S., France and a couple of other nations, is involved in cyber-war planning. Many international high-tech companies are now locating research and development operations in Israel, where local hires are often veterans of the IDF’s elite computer units. In September 2007, Israel carried out an airstrike on Syria and reportedly used cyber-warfare to allow their planes to pass undetected by radar. Following US decision to pull out of the Iran nuclear deal in May 2018, cyber warfare units in the United States and Israel are monitoring internet traffic out of Iran and have noted a surge in retaliatory cyber attacks from Iran. Similarly Iranian hackers were sending emails containing malware to diplomats who work in the foreign affairs offices of US and its allies. Cyber-warfare in the United States is a part of the American military strategy of proactive cyber defence and the use of cyber-warfare as a platform for attack. They are clear that a cyber-attack is just as a traditional act of war. In 2013 Cyber-warfare was, for the first time, considered a larger threat than conventional terrorism. As a doctrine, the Pentagon has formally recognized cyberspace as a new domain in warfare as critical to military operations as land, sea, air, and space. In 2009, President Barack Obama declared America’s digital infrastructure to be a ‘strategic national asset’, and in May 2010 the Pentagon set up its new US Cyber Command (USCYBERCOM) to defend American military networks and attack other countries’ systems. EU and UK have also set up a cyber-security operations centers. The government and corporate infrastructures will continue to be defended by US Department of Homeland Security and private companies themselves. China has plans of winning information wars by the mid-21st century. Others like Russia, Israel, Iran and North Korea are also having Cyber Armies. The PLA is having dedicated ‘information warfare’ units to develop viruses. Cyberspace technology is emerging as an ‘instrument of military power’. With low barriers to entry, coupled with the anonymous nature of activities in cyberspace, the list of potential adversaries is broad. Cyberspace will become a main front in both irregular and traditional conflicts. The United States has used cyber-attacks for tactical advantage in Afghanistan and against North Korean missile program.

Chinese Cyber Warfare Ability
Nearly 120 countries have been developing ways to use the Internet as a weapon. China’s ‘hacker army’ is known to have be 100,000 experts. China is using access to Microsoft source code and ‘harvesting the talents of its private sector’ to boost its offensive and defensive capabilities. They have had a number of high-profile cases of espionage, primarily through the use of a decentralized network of students, business people, scientists, diplomats, and engineers from within the Chinese Diaspora. Reportedly there are over 1,000 Chinese cyber spies. Chinese targets in the United States have included aerospace programs, including Space shuttle, C4ISR data, high-performance computers, nuclear weapons design, cruise missile data, integrated circuit design, among others. Chinese are also targeting India, Russia, Canada, and France. China’s main target is to acquire foreign military technology. Chinese government uses new space-based surveillance and intelligence gathering systems, anti-satellite weapons, anti-radar, infrared decoys, and false target generators to assist in this quest. There is increased education of soldiers in cyber warfare. They have built many virtual laboratories, digital libraries and digital campuses. China’s technological capabilities are being linked to the beginning of a new cyber cold war. The exposure of the People’s Liberation Army (PLA) Unit 61398 in Shanghai by the Mandiant cyber security firm highlights the PRC’s ability and willingness to conduct cyber exploitation and cyber attack operations globally. The PLA is actively creating the strategic guidance, tools, and trained personnel necessary to employ computer network operations in support of traditional war-fighting disciplines. PLA’s assessments of current and future conflicts note that campaigns will be conducted in all domains simultaneously but that its emphasis on the electromagnetic spectrum has driven the PLA to adopt a much more comprehensive approach. The Chinese strategy known as integrated network electronic warfare combines electronic warfare, computer network operations, and kinetic strikes to disrupt battlefield information systems that support an adversary’s war-fighting and power-projection capabilities.

Legal Issues
There is still no widely accepted international legal framework. The Shanghai Cooperation Organization (SCO) has defined cyber-war to include dissemination of information ‘harmful to the spiritual, moral and cultural spheres of other states’. In contrast, the United States’ approach focuses on physical and economic damage and injury, putting political concerns under freedom of speech. A Ukrainian professor of international law, Alexander Merezhko, has defined cyber-warfare as the use of Internet and related technological means by one state against the political, economic, technological and information sovereignty and independence of another state. A “Digital Geneva Convention” has also been proposed.
India’s National Cyber Security Policy -2013 (NCSP) and Structure
The NCSP recognizes that Cyberspace is a complex environment supported by worldwide distribution of information and communication technology devices and networks. Policy will be approved and put into force shortly. Because of immense benefits, the cyberspace is used by citizens, businesses, critical information infrastructure, education, health services, military and governments, among others. Cyberspace is expected to be more complex in the foreseeable future, with many fold increase in networks and connected devices. There therefore was a need to create suitable cyber security eco-system in the country. Large-scale cyber incidents may overwhelm the government, public and private sector resources and services. The plan is to protect information and information infrastructure in cyberspace, build capabilities to prevent and respond to cyber threats, reduce vulnerabilities and minimize damage from cyber incidents. The Department of Information Technology created the CERT-In in 2004 to thwart cyber attacks in India. In 2011, there were 13,301 cyber attacks, therefore India created a new subdivision, the National Critical Information Infrastructure Protection Centre (NCIIPC) to thwart attacks against energy, transport, banking, telecom, defence, space and other sensitive areas. It operates 24×7. A high-profile cyber attack on 12 July 2012 breached the email accounts of about 12,000 people, including those of officials from the Ministry of External Affairs (MEA), Ministry of Home Affairs (MHA), Defence Research and Development Organization (DRDO) among others. The Cyber threat is overseen by the National security Adviser (NSA). India faces an acute shortfall and needs thousands of experts. Many steps have been initiated that include the isolation of various security agencies to ensure that a synchronized attack could not succeed. On 26 November 2010, a group calling itself the Indian Cyber Army hacked the websites belonging to the Pakistan Army and the others belong to different ministries, including the Ministry of Foreign Affairs, Ministry of Education, Ministry of Finance, Pakistan Computer Bureau, Council of Islamic Ideology, etc. The attack was reportedly as a revenge for the Mumbai terror Attacks. Pakistan Cyber Army retaliated and hacked the website of India’s top investigating agency, the Central Bureau of Investigations (CBI).
Indian Military Networks
Indian Army currently has its operational systems integrated through the project ‘Akash Teer’ for situational awareness. Indian Army has recently given a ‘large’ contract for setting up an advanced IT-enabled system to operate the its network under the Network of Spectrum (NFS). It involves creating a centralised network monitoring, management and control system for all the seven layers under NFS which interconnects 414 Defence stations. The project involves the creation of a resilient Cloud-based IT infrastructure on Infrastructure as a service (IAAS) model. The facilities under this project will allow real-time monitoring of the complete IT network backbone of the Indian Army and provide complete visibility of deployed Network assets.

Indian Navy’s indigenous maritime awareness and mission planning networked system “Trigun” is maturing. The Indian assets will be well informed about all kinds of merchants ships, warships, submarines and aircraft around the Indian assets. This system will be the most modern and sophisticated phase of the Maritime Domain Awareness Program. The third phase, planned between 2020 and 2024, will have integrated Artificial Intelligence and Data Analytics and will have a integrated naval common operational picture. The Trigun System has been designed and developed indigenously by the Centre for Artifical Intelligence and Robotics (CAIR) functioning under the DRDO aimed to enhance battlespace transparency with better network-centric warfare tools riding on high-speed data communication systems and their integration.
The Indian Air Force (IAF) made progress towards becoming a truly network-centric air force with the integration of Air Force Network (AFNET), a reliable and robust digital information grid that enables accurate and faster response to enemy threats, in 2010. The modern, state-of-the-art AFNET is a fully secure communication network, providing IAF a critical link among its command and control centre, sensors such as the Airborne Early Warning and Control Systems, and attack platforms such as fighter aircraft and missile launchers. Integrated Air Command and Control System (IACCS), an automated command and control system for Air Defence (AD) operations rides the AFNET backbone integrating all ground-based and airborne sensors, AD weapon systems and C2 nodes. In October 2013, IAF launched its own stand-alone cellular network, through which secure video calling and other information exchange facilities will be provided.

Defence Communication Network (DCN) is the first tri-service communication and IT network of the Armed Forces. The hi-tech, fully secure DCN is the largest single satellite network spread across the country. This integrated communication architecture between the Army, Navy and Air Force bolsters the prowess of the Defence forces during both critical operations and rescue missions. DCN also supports IDS and SFC. It had drawn a lot of ideas from the AFNET.

Defence Cyber Agency (DCA)
The tri-service Defence Cyber Agency (DCA) of the Indian armed forces Headquartered in New Delhi was established in on 28 September 2018. It is mandated with the defensive, deterrence and offensive aspects of cyber warfare. DCA is tasked with handling cyber security threats, and it draws personnel from all three branches of the Services. It is a major step based on the recommendations of the Kargil Review Committee, and indicates the seriousness India finally attaches to cyber threat and its fallouts. The head of the DCA is a two-star officer and he reports to the Chiefs of Staff Committee through the Integrated Defence Staff (IDS). In May 2019 Indian Navy’s Rear Admiral Mohit Gupta was appointed as the first head of the DCA. DCA will initially directly employ about 1,000 people drawn from the Indian Air Force (IAF), the Army and the Navy, besides from the Integrated Defence Staff (IDS) and will be a precursor to the setting up of a cyber command in the future. The DCA is now fully operational. It will engage in defending military assets and resources and also use its offensive capabilities in proxy cyber warfare like those being indulged in by non-state actors and terrorists. The DCA would have the capability to hack into networks, mount surveillance operations, lay honeypot, recover deleted data from hard drives and cell-phones, break into encrypted communications channels, and perform other complex objectives. The IDS will ensure synergy and inter-linkages among the various constituents of the military. Besides looking into forensics and other verticals, the DCA will audit based on potential risks and threat perceptions. It will have key linkages with the agencies dealing with cyber crime issues. DCA would exploit and utilize the technology available with the country’s rich resources base of young software entrepreneurs and technocrats. The DCA will have the responsibility of framing a long-term policy for the security of military networks, which includes eliminating the use of foreign hardware and software. DCA will also be responsible for preparing a Cyberwarfare doctrine. Cyber warfare domain is already live and any aspiring power has to build capabilities and keep abreast of the developments.
This Article was written by me and first published by Centre For Joint Warfare Studies (CENJOWS. It has since been significantly updated.
Picture Credit: info-stor.co.uk


5 thoughts on “Cyber Warfare a Key Element of Multi Domain Wars – Time to Push India”